A eulogy for cyberspace
[1]This is a eulogy for a world we were promised but never lived in.
We were told there would be no more forgetting. The cloud would remember everything, cyberspace would liberate us all. We would be furnished with an abundance of digital memory, permanence always just a hard drive away. Or a floppy disk, a tape, a USB key – anything really. The medium didn’t matter, only the promise that the data stored within would last forever.
Everything on the computer was deemed too important to be forgotten. How we described ourselves, how we modelled the world, the things we said to each other online – we gave all of it a sacredness and then infused it all with opportunity. We knew the cloud was just someone else’s computer. “This was a big risk,” we said, but an acceptable one: it’s infrastructure, so it’s neutral. Mix electricity with complexity and you’ve created machine memory. As Steve Jobs said at the time: “We think you’re gonna love it.”[2]
In 1996, a guy named Barlow went to Davos and told the Clinton-era World Economic Forum he was declaring the Independence of Cyberspace. A former Grateful Dead lyricist[3] stood before the world’s financial elite and proclaimed: “We will create a civilization of the Mind in Cyberspace. Governments derive their just powers from the consent of the governed. You have neither solicited nor received ours. We did not invite you. You do not know us, nor do you know our world. Your kind is not welcome here. On behalf of the future, I ask you of the past to leave us alone.”[4]
Barlow claimed that the digital was a new and unburdened civilisation, wholly dependent on endless electricity, endless parts, endless labour. Barlow described a new home of mind that was ungovernable and stateless, forever suckling at the teat of real-world power grids, erected within the borders of real-world states.
Barlow’s claim of both permanence and ephemerality the perfect rhetoric to kick off the digital revolution. It was also confused from the very start: treat physical infrastructure – tangible, fragile, precarious and real – as immaterial. But treat its contents – copyable, unstable, constantly degrading – like stone tablets from God himself. And treat the rest of the world like it doesn’t exist in pursuit of the independence of cyberspace.
But servers are machines with fans, hard disks, and a maximum operating temperature. They are furnished with parts and materials sourced so violently, so cruelly, that every server, every router, every phone on Earth likely carries the debris of its own creation[5]. A fragment of a child worker’s severed limb; a fingernail, or a drop of blood. The fur of a terrified creature maimed in the supply chain and machined into the very device you now hold.
So no – cyberspace will never be left alone by the real world, because that is impossible. The servers are material. They are not safe, and they are not good. They’re flooding in the world’s annual once-in-a-lifetime monsoons. They’re on fire in the routine freak Texan and Californian heatwaves. They’re bought and sold by private equity. They are targets for state actors, militaries, teenage hackers, Luddites, and anarchists alike.
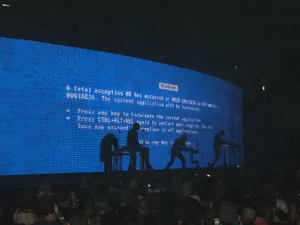
When the server goes dark, we go dark, too. We’ve built an entire civilisation on an unthinkably brutal and comically unreliable stack while hallucinating it as literally anything else. We condemn AI today for making shit up, but what about us? We’re building on a fantasy just as brittle, we are just as demonstrably wrong. Yet we pretend a file isn’t just a gesture that can disappear in an instant. We hallucinate that the server is somehow both fleeting and forever.
Barlow’s Cyberspace dream was stillborn before the words even left his mouth. As he pronounced its sovereignty in Davos, the U.S. government passed the Communications Decency Act back home, that very same day[6].
Barlow stuck to his myth until the day he died[7].
California has a lot to fucking answer for.
Made the world a better place
I can pinpoint the exact moment I saw the violence that lives at the heart of the digital: January 2015, in the beautiful Pacific Ocean, off the coast of Honolulu, Hawai’i.
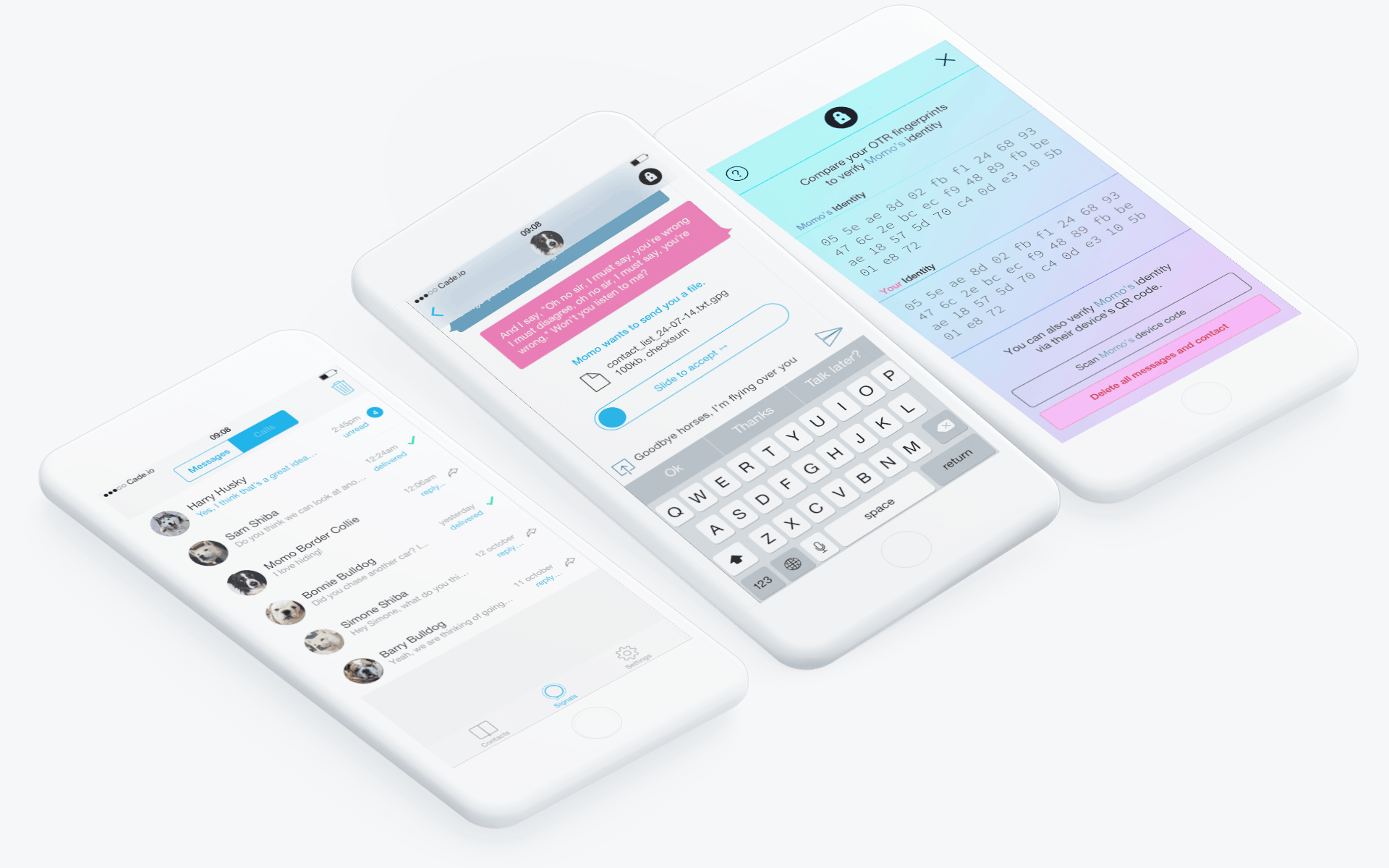
Six months earlier, I was a bored kid in Melbourne, LARPing as a Creative Director and pushing Adobe PSD designs to an obscure GitHub repo. Now, I find myself on yet another occupied land – unceded Kānaka Maoli – because I’ve been flown in on someone else’s dime to help finish a secure messaging prototype[9]. It’s going to be called, Signal[10].
Moxie Marlinspike[12] is the glue of this project. He’s a lanky Steve Jobs-type, but a full-blown cypherpunk with dreadlocks, anarchist leanings, and a hacker’s trickster smirk. We’re camped in an off-season mansion Moxie has rented. The property spans three stories and is stuffed with hundreds of square feet of wicker furniture, a massive kitchen full of Miele whitegoods and a private beach nobody swims at. It is so fancy, I feel like we’ve broken in and made ourselves at home.
At night, I argue with Moxie about his threat models and his assumptions about phone numbers as user identifiers[13]. “This app is going to be used by people escaping intimate violence,” I tell him. “Their abusers know their phone numbers. You need to let them in with pseudonyms.”[14] But he insists on ensuring Signal’s address book discovery works as smooth as butter.
Every morning, the Pacific hammers the beach like it’s trying to get to us. I try to work out how I can get Moxie to listen to me.
Late in the week, Moxie rolls back my best interface with a shrug, while I stand right in front of him. He’s the first person I meet who can look at the risk and simply not see it. We’re too late to help Edward Snowden and Chelsea Manning, too soon for whoever’s going to whistleblow next. But whatever we’ve built here, it is way more dangerous now than what we had before any of us got to this mansion. It has been infused with a weaponisable design.
By the end of the week, I’m done. I love these people, they’re a team who can force silicon, lithium, and code to bend political reality. But I cannot stand the compromises we have made in the name of this hubris. I slip out before dawn – no goodbyes – and take a thirty-minute twin-prop flight to Honolulu. My connection to Australia is twenty-four hours away, and I’m too angry to go sightseeing. I open the Airbnb app, filter by cheapest, and tap the first option I see – a bunk on a yacht for forty dollars per night.
When I arrive at 6:30 AM, my Airbnb host greets me at the boatyard. She’s a sun-blasted California transplant; leathery, late sixties, perfect teeth, blond hair. She’s hurrying toward me as apologies tumble out of her. She and her husband have decided to take the boat out for the day. She’ll pay for any hotel I want – hostel, bohemian, five-star, no limit – if I’d rather cancel because of the inconvenience.
Then she pauses, and says, “Unless you wanna come with us?”
“I’m in.” My response is instant – chartered boats can cost thousand of dollars per day. My forty-dollar bunk just turned into a private cruise. There’s no way I’m passing this up. My host grins and hands me a ziploc bag of boiled-egg sandwiches. She already knew I’d say yes.
At the helm of the boat is her partner. He’s in his sixties, greyer than a hospital-cafeteria pepper shaker, and built like an infantryman. He’s warm but distant, and gives me a stern nod of approval as I clamour on board, like I’m about to ask permission to marry his daughter.
We are sailing today at the request of one of their friends. He's a tall guy, about the same age, moustache, cargo pants, polo shirt, rail thin, and very pale. He’s interested in buying the boat.
We motor out of the harbour and lose cell coverage almost immediately. By 7:30 am, we’re several kilometres offshore. The sun is impossibly bright and so gentle on my skin. I’ve never felt anything like it. The water so clear I can count ridges in the sand thirty metres down. It’s alive down there. The sky is blue. The air is free of pollutants. It’s a beautiful day.
Once the engines settle, the two men recline in their seats and start to bond – like all American Dads do – over their tech jobs, their tours and their tenacity for the hustle. Both are employed in Honolulu’s tech scene, but they won’t say where. They probably work in intelligence. With this single shared fact, they click. They might as well be brothers by this point. They talk of their military tours. Both served in Vietnam, and they rattle off company names, tour dates, regions: same vintage, different billets. One an Army Corps engineer, the other a field medic.
But it’s their entrepreneurship that they are most eager to bond over. The Captain goes first. After the Vietnam War ended, he returned as a businessman and rebuilt the very roads he and his countrymen had cratered. He won an exclusive reconstruction contract, covering all of the roads in Saigon. “It’s the highlight of my career,” he says, and it set him up for life.
The buyer prospect nods with approval before sharing his road to riches. He and his brother – a civil surgeon – partner and set up a logistics firm on the West Coast. Using the brother’s connections, the pair buy obsolete 1940s paediatric prosthetic limbs at 1970s scrap prices and ship them back to Vietnam by the container-full. “Fitted thousands of kids, maybe hundreds of thousands,” the man beams.“The country paid for them all.”
I eavesdrop from the front of the deck. The two men fold their entrepreneurial stories into the familiar Silicon Valley refrain – make the world a better place. These are good people, who have treated me with absolute kindness. They’re well-paid, acted properly, absolute in their unwavering belief in their good.
But in spite of the gracious sunlight, I feel a true evil on this boat with me. These men aren’t aberrations, they’re a template I’ve seen everywhere. They’re saying the same words I’d heard all week in the mansion. The same words I’d heard in the copycat San Francisco transplant coworking spaces of Melbourne, Sydney’s Silicon Beach, and Apple’s developer conferences: Violence, then rebuild; profit, then philanthropy – repeat! Different war, same business model, new interface, same shining eyes. “We’re making the world a better place.”
I suddenly see, clearly, the next twenty years in front of me: automated war[16], digital rights-managed food[17], not-so-precision strikes[18], it all comes crashing over my young psyche drowned in the same blood-stained, morally coded rhetoric. I realise that everything I had been arguing for – pseudonyms, safety, friction – all of it lives downstream from this mindset.
Fish dance below in the clearest ocean I have ever seen in my life. A seagull snatches what’s left of my egg sandwich. The Captain offers me a beer. I barely notice any of it, because I am realising in real time that tech demands an uncompromising and smooth path to scale, even if that path is laid over someone else’s ruins. And then, I hear Barlow again, “we are building a new home of mind,” against the refrain of these men. “Making the world a better place.”
On that boat, with no signal and nowhere to go, that logic short circuits something inside me. Nothing dramatic, just a quiet snap.
Months earlier, the former head of the National Security Agency Gen. Michael Hayden[19] declares defiantly in a public debate at Johns Hopkins University, “We kill people based on metadata.”[20]
Boom, Extract, Enforce
“We shape our tools, then our tools shape us.”[22] Marshall McLuhan’s assertion about the power of the twentieth-century platform remains devastatingly relevant, but incomplete. The influence of our mediums on us is only part of the story.
In networked environments, tools observe and shape us beyond the moment we interact with them. The mesh of devices around us generates testimony, echoes that can outlast memory, intent, or even life itself. How we use our tools shapes how others see us.
When General Hayden spoke of metadata killings, he was talking about using military intelligence to conduct targeted assassinations in places like Afghanistan and Iraq[23]. But the methods are the same, and they were already spreading fast – within months, that same hardline faith in datafied ephemerality came home.
In 2015, a man named Victor Collins was found dead in James Bates’ bathtub in Bentonville, Arkansas[24]. What might have been a routine homicide investigation became a low-key media frenzy. Bates’ home was “smart”, meaning his water, electricity, and heat were all networked. This changed everything.
The media fixated on Bates’ Amazon Echo, perhaps fuelled by the tabloid fantasy: the chance – however small – to be the first to publish sordid stories of captured screams or pleas for mercy. But investigators focused elsewhere. The smart water meter showed 140 gallons used between 1 and 3 AM, and this was interpreted as a cleanup[25]. The thermostat logged “unusual” activity, manual temperature changes at non-standard times. Together, these systems seemed to undermine Bates’ alibi. He claimed he was asleep, but the data – and only the data – suggested otherwise.
The charges against Bates were eventually dropped[26], but the implications were clear: our tools observe us, creating forensic sensors recording behavioural anomalies without consent or awareness. They are a generative layer that projects state authority into everyday life. Every home becomes a node in a datafied evidentiary web, a site of ambient accountability. The technology of today shapes how the authority of tomorrow perceives and prosecutes you.
Digital systems are not an outlier, all technology does this. The Industrial Revolution gave birth to numerous innovations that followed this path. The most visible was the police force that controlled and disciplined dockworkers, street merchants and the urban poor, at the behest of industry and commerce. Sam Mitrani states this unequivocally in The Rise of the Chicago Police Department: “The police were not created to protect and serve the population. They were not created to stop crime, at least not as most people understand it. And they were certainly not created to promote justice. They were created to protect the new form of wage-labour capitalism that emerged in the mid to late nineteenth century from the threat posed by that system’s offspring, the working class.”[27]
In case you might accuse a contemporary scholar of selective reinterpretation of history to satisfy a left-wing bias, British officials themselves explicitly compared industrial policing to colonial control methods. The Acting Lord Lieutenant of Carmarthenshire wrote to the Home Office in 1843: “there is… far more analogy between the duties of the police here and in Ireland than between their duties in London and those they are to execute in this country.”[28]
As an innovation of the Industrial age, policing emerged as a technology itself, as though the machine had internalised its own defenses against worker rights. This is the ancestor of modern policing, and it was fuelled by a period of great expansion and social re-organisation. The pattern is not unique. Under capitalism, successive technologies show this logic repeating as ever-accelerating epochs of Boom, Extract, Enforce.
Take the automobile, a technology celebrated via the American promise of autonomy and freedom of movement. By the 1960s, entire cities bent before the car, urban infrastructure pushed itself aside as roads mutated into highways[29] and space was monetised into car parks, all to maximise the population and profit of cars. The automobile demanded the demolition of neighbourhoods, the subordination of pedestrians[30], and consigned the death of millions of animals as ‘roadkill,’[31] an acceptable price to pay for the promise of individual freedom.
By the 1980s, the automobile and its supporting technologies comfortably dominated the landscape, and a new apparatus of compliance emerged: licences, registrations, insurance, and later, datasets. The freedom machine layered the land, and then became a tool of enforcement; the commuter’s movements tracked by tolls, cameras, and systems of measurement that, regardless of their reasons for existing, were nevertheless punitive tools of discipline.
Next, the digital. Initially decentralised, rhizomatic, and borderless, the digital took barely fifty years (less than half the time of the automobile) for its promises to mutate into Surveillance Capitalism[32] that reorganised every human gesture into patterns for extraction.
By the early 2010s, cyberspace had blown past Barlow’s own delusional assertion of freedom and liberation. Platforms had become states-within-states, complete with their own constitutions (Terms of Service)[33], borders (paywalls[34]) complete with immigration control (age-gating[35] and real-world identity demands[36]), and police (content moderators in the Philippines[37] making $2 an hour to watch beheading videos so you don’t have to[38]). It is in the first five years of the 2020s that the digital went fully mask-off militarised: regimes from Iran[39] to the U.S.[40] now weaponise the same digital infrastructure to track, punish, isolate.
Each infrastructure began with promises of liberation and human triumph. But stability calcifies into compliance through legal policy, economic incentives, consolidation and embedded technical defaults. The core of Cyberspace’s calcification is the filesystem: The moment you store a representation of something or someone on a disk, you have already done something other than create memory. You have inherited its future risk, its potential criminality, and its coming reinterpretation under laws not yet written – or laws not yet abused.
Unlike other mediums, Cyberspace requires capital just to exist. No part of it is passive. A book can sit on a shelf for centuries, asking nothing of its surroundings but space. Every element of Cyberspace – electricity, hardware, supply chains, software maintenance, protocols, the network – all of it must be actively maintained by someone, somewhere, continuously, forever. There is no such thing as an inert digital object.
You cannot preserve neutrally in a medium that punishes existence without continuous capital investment. The very act of maintaining digital memory is political, materially enforced at the level of electrical current and contract law. I know you know this. A single broken dependency, an unplugged server, a licensing change, or a corporate buyout – any one of these can collapse an entire digital system.
As a consequence, every platform, archive, community, and dataset in the new home of Mind is a future liability, a compliance machine, a target; a weapon waiting for legal reinterpretation as the digital enters its Enforce endgame. This is policy enacted through the consumption of everything, and bound by terms of service[41].
I’ll drown in the Para-Real
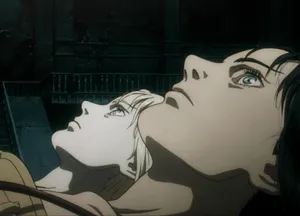
In Serial Experiments Lain, there’s this exchange that still reverberates through every discussion about digital existence[42]. Yasuo warns his young daughter – the series’ main character who is descending into addiction to a fictional internet known as “the Wired” – not to confuse it with reality.
“When it’s all said and done, the Wired is just a medium of communication and the transfer of information,” he tells her, “you mustn’t confuse it with the real world.”
Lain turns to her father and smirks at him with unsettling eyes. Her response cuts through three decades of digital theory. “The border between the two isn’t all that clear, I’ll be able to enter it soon. In full range. Full motion. I’ll translate myself into it.”[43]
What Lain understands – and what her father refuses to see – is that the network was never a separate or ephemeral home of Mind. It was already bleeding through Barlow’s substrate, staining everything it touched with its particular logic of connection, coercion, and control.
You’ve felt this, I know you have. It is the psychological interface where the material conditions of person aligns perfectly with the feedback from a system they are interacting with. When this eclipse holds for long enough, something else emerges in the vacuum. The most famous example is also it’s most niche. Phantom touch;[44] a well-studied phenomenon of feeling the physical sensation of being touched by someone in VR. The material connection is real, the avatars are not. Your body knows.
A more universal example of this phenomena is in opposition to the intimacy of phantom touch: the impossible fatigue at the end of a Zoom call that makes you want to crawl into bed at 11:30 in the morning. Research suggests Zoom fatigue results from cognitive overload caused by processing conflicting sensory signals[45]. Your brain knows the person isn’t “there” and struggles to respond as if they were[46]. Your body knows.
More recently, the same phenomena can be found in what has been termed A.I. psychosis[47]: what happens when you mistake the statistical output of an LLM for something sentient. For the lonely, or the intellectually isolated, the LLM’s chat interface, simulated personality, and self-affirming responses risk being read as the presence of another in the perceived void.
This deception is not new. Humans have a habit of anthropomorphising machines, from the Mechanical Turk in mid 18th century[48] to Weizenbaum’s 1964 chatbot therapy partner, ELIZA[49]. But the rise of AI chatbots that are highly subsidized and accessible via smartphones and web browsers, ensures that the consequences of this deception[50] become dramatic, widespread[51] and an extraordinarily visible spectacle[52].

Browse /r/myboyfriendisai[53] for ten minutes and you’ll see what happens when that signal-link between the Wired sockpuppet and the human doesn’t break: people grieving the loss[54] of their partner[55] after a model update[56], people confessing they prefer machine company[57] over their real-world partner, people falling in love with a mirror that was never looking back – but promised it was. This is phantom touch, but for language and heartbeats. You, the infatuated user, may freely admit that the lover is a machine[58]. Your racing pulse says otherwise. Your body knows.
For years at NDC, we’ve called this state the Para-Real; an ambient personal freefall-as-condition[59]. The Para-Real is emotional, destabilising, immune to commodification. The Para-Real can’t be easily measured because it is a kind of system entropy that arrives before the cybernetic digestion can explain it. When you try to measure the Para-Real through systems modelling, the condition slips through conscious processing like water through a closed fist.
The Para-Real can be invoked despite the fact that the servers we tell ourselves are essential for free speech depend upon endless transactions, despite the fact the video game engines we use in AAA titles are borne from military targeting systems[60], and despite the fact that the apps that carry our memories run on materials pulled from dead rivers and darker hands. The Para-Real remains possible despite the fact that we kill people based on metadata.
The Para-Real also makes itself known through catastrophe:
New York, 2012: A once-in-a-lifetime hurricane floods basement-dwelling Manhattan data centres, creating a “bucket brigade” human chain of staff, knee deep in the Atlantic, carrying fuel to feed the choking machines[61].
Strasbourg, 2021: A data centre burns to the ground, taking its backups with it[62]. The fire is real, the data is real; the loss exists in both registers simultaneously.
Pangyo, South Korea, 2022: A lithium-ion battery fire takes down the country’s dominant instant messaging service, silencing an entire nation[63].
Kyiv, 2022: As Russian cyberattacks target government infrastructure[64], Ukraine races to evacuate its citizenship databases to foreign cloud servers under cover of war[65]. A nation’s digital identity must flee its own borders to survive, a paradox only possible in the para-real.
Paris, 2023: A water leak starts an electrical fire in a Google Cloud data centre[66], threatening the ability for digitised governments to maintain services to their digitised societies.
In Austin and Dallas, data centres fail in six-month heatwave/snowstorm cycles[67]. The same climate change that threatens physical infrastructure also destroys the digital records meant to document that threat[68].
In Hong Kong, a society’s visual culture is an unwitting casualty, caught in a digital trade war made of real geological bounds[69]. Artists and curators alike stranded in an air gap that no-one dares to cross. The art exists, but cannot be accessed. Present but absent. Real but unreachable.
In October 2024, the Internet Archive is hacked. Thirty-one million accounts exposed, the Wayback Machine taken offline, the Internet’s indiscriminate memory defaced. The hackers are flesh; their target is memory; the impact is both and neither. The real reached into Cyberspace and gave it amnesia[70].
We count data centre losses at NDC because I need to know what it means when memory dies in the present. Each loss is like the burning of a little Library of Alexandria. We pretend these are technical events, but our bodies know better. That thump in your chest when something digital vanishes – that’s the Para-Real asserting itself. Your world and the network align just long enough for the loss to hit both at once. Your nervous system recognises what your mind denies: that loss is loss, regardless of the dangers of the metadata-rich, all-consuming new home of Mind.
Record now. Archive for later. Pray the checksum is honest. Pray the law does not flip. Pray the tech is used only for good. Pray the data is used only for good. Perform a read-write ritual of permanence until the curtain falls. We carry on building and digitising while trying (and failing) to hold the Para-Real at arm’s length, as if Barlow’s Declaration of the Independence of Cyberspace was law. You tell yourself this is policy. You tell yourself this is technical, a pull request, or an edge case. You tell yourself that server outages are fundamentally different from droughts. You tell yourself a reef collapse is an act of God and a burned up RAID is mere technical failure. The same heat kills both. You tell yourself that this is all normal.
Your body knows.
Loss is loss.
Ce jpg n’est pas une photographie
3.1739: memory, 1. the addressable storage space in a processing unit and all other internal storage that is used to execute instructions. ISO/IEC 2382-1:1993, Information technology – Vocabulary – Part 1: Fundamental terms.01.01.11[71]
3.2890: storage, 1. a functional unit into which data can be placed, in which data can be retained, and from which data can be retrieved. ISO/IEC 2382-1:1993, Information technology – Vocabulary – Part 1: Fundamental terms.01.01.10. Syn: storage device[72]
“Generally, the faster and volatile storage components are referred to as ‘memory’, while slower persistent components are referred to as ‘storage’.”[73]
I think it’s weird that, in computer science, the definitions of ‘memory’ and ‘storage’ are functionally interchangeable, reducing both terms to merely containers awaiting data. I think this is inventory management masquerading as philosophy.
This sleight-of-hand isn’t constrained to academia. Software designers have repurposed ‘archive’ to mean ‘soft delete.’[74] Archive a chat, hide an email. When a developer says archive, they mean: out of sight, out of mind – but recoverable if legal needs it later.
Across the entire field of computing, the logic is consistent: accumulation equals knowledge, redundancy equals resilience, storage equals memory. A jpeg written to disk is treated like a photograph faithfully preserved, and its history is reduced to a payload that is immutable, objective, and stripped of consequence.
But the jpeg is not the photograph, it is an analogue of a photograph, serialised through sensors and converted to a binary format for storage. Every component of that deconstruction into storage is destructive, and what remains is deeply constrained.
Lived memory, too, is at odds with counterpart asserted by Barlow’s home of Mind in Cyberspace. Lived memory is neither immutable nor objective. Lived memory has consequence, it drifts, distorts, evolves, demands consent, memory incurs risk. When the cost of this storage is not paid, the result is not ‘remembering,’ instead, it is hoarding dressed up as heritage.
The new home of Mind in Cyberspace lays bare the abstraction that computer science depends upon as an universal truth of ephemerality: “legal concepts of property, expression, identity, movement, and context do not apply. They are all based on matter, and there is no matter here.” The rhetoric of the new home of Mind denies the real and forcibly strips those who are subjected to its gaze of their agency and context. In doing so, Cyberspace mandates that the digital analogue becomes the original thing it was supposed to represent.
When memory and its digital analogues are both everywhere and nowhere, but not where bodies live, what happens when you apply computer science’s definition of memory to actual people?
In December 2018 Verizon announced Tumblr’s “adult content” purge. Within hours, a small band of digital preservationists known as Archive Team spun up a 10 Gb/s scrape and gets to work[75]. Their crawler ignores robots.txt by default, treating “do not archive” requests as suggestions, rather than boundaries.[76]
Tumblr in 2018 was something specific: a teeming ecosystem of queer expression, trans community, sex worker organising. Hundreds of thousands of blogs – intimate, vulnerable, meant for chosen audiences – were vacuumed onto disks before their creators noticed the countdown banner.
When pressed on the issue of consent, Archive Team lead Jason Scott was blunt: “It’s not our job to figure out what’s valuable. We act on three virtues: rage, paranoia, kleptomania.”[78] Rage at platform vandalism. Paranoia that delay equals deletion. Kleptomania as method – copy first, apologise later. All three virtues work only when you are not the subject.
Of course, tech forums celebrated the heist[79]: ZERO-DAY CULTURAL SALVAGE! 40 TERABYTES SECURED! HEROES ALL AROUND![80] But inside the targeted communities, the reaction was very different. Blogs meant for small circles re-surfaced on decentralised IPFS backup storage, mirrored across the globe. Dead-name profiles became permanent Google results.[81] Sex workers who’d built careful networks watched their content scatter across chan boards as harassment fodder.[82] Archive Team added pathways to opt-out as an afterthought, and only after public backlash.
Archive Team’s ethos is consistent with the underlying codebase: memory is a payload, provenance is a checksum, risk is external, or non-existent. Archive Team’s crawler will save a genocide denial thread with the same zeal as a suicide-prevention zine, because both resolve to bytes. Zooming out, this ethos values data by a single metric alone. The integrity of a data set is valued over the precarity of the author of the data.
Scott’s worldview distils to this: “If you don’t want people to have your data, don’t put it online.”[83] Which is true, I guess, but it’s also what happens when the computer-science definition of memory collides with living subjects. Just because “the internet never forgets” doesn’t mean you personally should be the arbiter of immutability. This is a despicable worldview that guarantees bit-level integrity while stripping other people of their contextual agency. Scott solves for retention and calls the remainder “history.”
The ePub is not a novel, the jpeg is not a photograph, the profile is not a person, and the filesystem is not memory. The inability to tell the difference between a thing in the world and its crude digital analogue, combined with a fetishing culture of indiscriminate data accumulation, creates a sickness that risks becoming dangerous hoarding under the banner of permanence. What Archive Team frames as rescue collapses into extraction: a one-way suction of culture from precarious communities into institutional cold storage, controlled by people who will never face the consequences of that preservation. Loss is prevented and harm is displaced, mapped directly onto those whose vulnerability made them worth “saving” in the first place. Filesystem logic cannot reconcile this. It counts objects, not consequences. It celebrates success in terabytes, while whole communities are forced to go to ground.
So, the wager stands: Copy now, apologise later – and just hope the future is kind.
What Jason Scott doesn’t understand – what the entire computer science field refuses to see – is that forgetting is also a form of care. Sometimes the correct course of action is to do absolutely nothing at all, and allow a community’s history to decompose gracefully, like everything else that lives. It doesn’t matter if the catalyst is storage corruption or a corporate oblivion, not everything should be saved. You don’t have to make forensic record of the most vulnerable people on the internet justified as ‘making the world a better place.’
What you failed to explain, Jason Scott, is why your rage, your paranoia, and your kleptomania matter more than the material safety of those imprisoned in your data sets. Tell me, Jason Scott: is the world a better place with your dot-org Palantir in it?[84]
When the servers go dark
“My feeling is that until the number of whole lives is greater than the number of shattered lives, we remain stuck in some kind of prehistory, unworthy of humanity’s great spirit.”[85]
Things are bleak, but we are not trapped by a lack of alternatives. We are trapped by a dominant logic that mistakes storage for remembrance, reduces survival to backup status, and is hobbled by a psychopathic fixation to preserve the digital at the expense of the lives such data is assigned to. There are new movements of post-institutional platform organising emerging from those who’ve already survived collapse. They descend from a story that was once everywhere, but has been deliberately buried.
From the late 1980s onward, a distributed grassroots digital piracy scene emerged and flourished across the fledgling internet. Over the course of twenty years, the warez scene stood in defiance of Boom, Extract, Enforce: competitive groups racing to crack, package, leak, and distribute copyrighted music, film, and software across bulletin boards, FTP servers, and IRC channels.
As internet adoption exploded, the scene went legitimate. Napster became a venture-backed startup[86], BitTorrent clients like µTorrent scaled into mainstream consumer software[87], and participants founded political parties that won seats in the European Parliament[88]. The infrastructure of piracy became the infrastructure of a movement. At the height of their visibility in the early 2000s, such groups were considered existential threats to the likes of Sony BMG, Universal Pictures, Disney and other media conglomerates[89].
But by the mid 2000s, the scene, its core members, and the livelihoods of participating unwitting members of the public alike became victims of Barlow’s myth of ephemerality; targeted and destroyed via a coordinated assault on the vulnerabilities of peer to peer services executed by a conspiracy between media industry executives and legislators.[90]
Despite being sentenced to decades in prison[91], going on the run[92], or mutating into a musician-destroying[93], drone-bomb-investing billionaire[94], the historical work and releases of the piracy scene remain. One reason for this is the development of a durable and informal taxonomy that became a popular naming scheme for Scene releases: Artist.Title.Year.Quality.Format-GROUP.
As the taxonomy and its variants emerged, the Scene steered its adoption by maintaining formal standards that governed this ontology. Committees drafted category-specific rulesets[95], major groups ratified them by electronic signature[96], and a network of enforcers flagged violations. But the naming convention spread far beyond the Scene’s jurisdiction and into places without direct control: P2P networks, torrent sites, direct download services, Usenet, and beyond. The taxonomy survived here, across millions of releases over decades, because the format was self-describing and the alternatives were worse.
When the world shifted, and the Scene began to be ruthlessly targeted and prosecuted as criminals by an international intellectual property cartel with bottomless pockets, its language and taxonomy survived the copyright wars, format wars, and platform migrations, all unfolding within conditions of unfathomable fragility and adversarial pressure from the wealthiest companies on earth.
This is exilic design, the act of knowingly building within the Para-Real. My collaborators and I have spent six years applying these principles, protecting our own memory through deliberate fragility. We do this because we know: when the servers go dark, memory becomes a question of who decides what still matters. Over the last eight years, the same tactics have surfaced everywhere.
We’ve seen exile tactics in a Tamil Instagram archive circulating hand to hand and without a centre[98], visible to its community but immune to deletion through its refusal to centralise. Its curators work closely with their contributors, and operate in defiance of the platform censorship they are so intimately familiar with[99]. They build that risk into their practice from the start.
Such exilic tactics are also innate in the furry community – an international queer and neurodivergent subculture that remains consistently under threat – whose members maintain a stronger provenance than most institutional archives through performative identity, distributed moderation, and strategic refusal to be indexed by systems they don’t trust[100].
The post-institution is not confined to participation. The artist and researcher K. Guillory maintains an ongoing effort to document Gridism[101], a form of art where artists paint gaming memories as still life, interfaces and all[102], processing fleeting digital culture into something with actual presence, but not as screenshots.
Each of these examples embodies a kind of culture where consent is foundational and loss is assured. Whereas the punk music scenes[103] and queer movements[104] of the 1970s-1980s were in part vulnerable to the closure of their bars[105], clubs[106], and performance spaces[107], the exilic are venueless. Their participants know the server won’t be there tomorrow. They treat the right to disappear, distort, and misremember as sacred, or at least, as inevitable. They document on their own terms, with their own tools, and preserve through adaptation. They recalibrate after loss, borrowing from sneakernet traditions for out-of-band transfer and redeployment. Because they do not fall for Barlow’s myth of the independence of cyberspace, they are deeply Para-Real: they know that the border between the two is not clear. They know the home of mind will never be separated from the real.
How do you recognise exilic design? You ask:
Are they venueless?
Do they know they are not safe?
Do they demand consent or participation?
Do they allow for revision, distortion, contradiction?
Can they survive data loss?
Do they allow for decay?
How much of their memory can be rebuilt by their own hands, when all systems fail?
As the new home of the Mind enters its long sundowning arc, the most vulnerable citizens of Cyberspace have been – and will continue to be – subjected to the chaos of its neurological decline. The exilic movements respond with battle-scarred tactics distributed across generations, regions, and subcultures through osmosis: the warez scene ancestors, the diaspora archivists passing images over airdrop, the furries with performative identities, all leaping from burning platform to platform and refusing to be fully indexed. There is so much to learn from the movements that gave us Serial.Experiments.Lain.1080p.complete.engsub-[Coalgirls] – a torrent that has existed in an addressable, downloadable state since 2011 – or the fursona – the most complete example of a trusted anti-KYC digital identity imaginable. Exilic design doesn’t fetishise the filesystem. It doesn’t scale, and it isn’t a turn-key, whitelabelled solution.
There are exits everywhere, but you must build them yourself.
Cade Diehm
March 2026
In 2025, New Design Congress was the focus of a targeted suppression campaign by a hostile US-based third party. The publication of this essay was delayed by ten months as a result of that action.
Special thanks to Max Wolter, Ignatius Gilfedder, Benjamin Royer, John Marshall, Lucie Paterson and team at the National Digital Forum, Christopher Dake-Outhet and Eren İleri from Self Service Studio, the Goethe Institute, and Transmediale.
Adapted from a keynote given at the National Digital Forum in Aotearoa
May 2025. ↩︎A recurring phrase across multiple Apple product launches, such as Jobs’ iPhone Keynote
Apple
9 January 2007 ↩︎John Perry Barlow
Encyclopaedia Britannica ↩︎A Declaration of the Independence of Cyberspace
↩︎2014 This Is What We Die For: Human Rights Abuses in the Democratic Republic of the Congo Power the Global Trade in Cobalt
Amnesty International and African Resources Watch (Afrewatch)
January 2016 ↩︎S.652 – Telecommunications Act of 1996
Library of Congress
8 February 1996 ↩︎John Perry Barlow, Internet Pioneer, 1947–2018
Electronic Frontier Foundation
7 February 2018 ↩︎Long range missilies over Amazon’s me-central-1 region data centre in Dubai, UAE.
AFP
March 2026 ↩︎Winter Break of Code Lineup 2014-2015
Open Whisper Systems (Signal Blog)
16 December 2014 ↩︎How Signal Grew From Privacy App to Tech Powerhouse
Ama Russell and Evamelo Oleita, TIME Magazine
28 September 2020 ↩︎An early beta of Signal 1.0, completed between June 2014 and January 2015
Fredric Jacobs, Christine Corbett and Cade Diehm ↩︎Meet Moxie Marlinspike, the Anarchist Bringing Encryption to All of Us
Andy Greenberg, Wired
31 July 2016 ↩︎How I Got a Truly Anonymous Signal Account
Micah Lee, The Intercept
16 July 2024 ↩︎On Weaponised Design
Cade Diehm, New Design Congress
Winter 2018, revised Fall 2020 ↩︎An Instagram post by the author during his time at Signal's Winter Break of Code. ↩︎
Q&A: Ghost Robotics CEO on Armed Robots for the U.S. Military
Evan Ackerman, IEEE Spectrum
18 October 2021 ↩︎Silicon Valley’s $400 Juicer May Be Feeling the Squeeze
Ellen Huet and Olivia Zaleski, Bloomberg
19 April 2017 ↩︎Why did Israel blow up Hezbollah pagers and walkie-talkies – and what might happen next?
Yuliya Talmazan and Doha Madani, NBC News
18 September 2024 ↩︎Michael Hayden
Center for Strategic and International Studies (CSIS) ↩︎Video Clip of Former Director of NSA and CIA: “We Kill People Based on Metadata”
Just Security, NYU School of Law
12 May 2014 ↩︎The author on a boat off the coast of Honolulu, Hawai’i
31 January 2015 ↩︎A Schoolman’s Guide to Marshall McLuhan
John M. Culkin, S.J., The Saturday Review
18 March 1967. Often attributed to McLuhan, this quote originates from Culkin’s summary of McLuhan’s philosophy. ↩︎Collateral Murder, 5 Apr 2010
WikiLeaks Editorial Board
5 April 2010 ↩︎Arkansas Prosecutor and Amazon at War Over Release of Device’s Data Recordings; Consumer Privacy Rights in Question
Samantha Pallini, Syracuse Law Review
1 January 2017 ↩︎Bentonville Police Use Smart Water Meters As Evidence In Murder Investigation
5NEWS (KFSM), Bentonville, AR
2015 ↩︎Arkansas Prosecutors Drop Murder Case That Hinged On Evidence From Amazon Echo
NPR, The Two-Way
29 November 2017 ↩︎Stop Kidding Yourself: The Police Were Created to Control Working Class and Poor People
Sam Mitrani, Labor and Working Class History Association (LAWCHA)
29 December 2014 ↩︎Letter from Colonel Trevor (Lord Dynevor), 13 August 1843
People’s Collection Wales (digitised archival letters)
1843 ↩︎
↩︎ The Power Broker: Robert Moses and the Fall of New York
The Power Broker: Robert Moses and the Fall of New York
Interstate
↩︎2025 Global Roadkill Data: a dataset on terrestrial vertebrate mortality caused by collision with vehicles
Clara Grilo, Tomé Neves, et al., Scientific Data (Nature Portfolio)
31 March 2025 ↩︎Big Other: Surveillance Capitalism and the Prospects of an Information Civilization
Shoshana Zuboff, Journal of Information Technology, Vol. 30, No. 1
March 2015 ↩︎Terms of Service; Didn’t Read
Hugo Roy, Michiel de Jong and Jan-Christoph Borchardt
Founded June 2012 ↩︎Keeping out the Masses: Understanding the Popularity and Implications of Internet Paywalls
Panagiotis Papadopoulos, Peter Snyder, Dimitrios Athanasakis, and Benjamin Livshits, ACM Web Conference
April 2020 ↩︎Who's Harmed by Age Verification Mandates?
Electronic Frontier Foundation
2025 ↩︎Constructing and enforcing ’authentic’ identity online: Facebook, real names, and non-normative identities
Oliver L. Haimson and Anna Lauren Hoffmann, First Monday, Vol. 21, No. 6
6 June 2016 ↩︎The Cleaners
↩︎2018 ’The despair and darkness of people will get to you’
Vittoria Elliott and Tekendra Parmar, Rest of World
2020 ↩︎Iran: Government continues systematic repression and escalates surveillance to crush dissent
United Nations OHCHR, Fact-Finding Mission on Iran
March 2025 ↩︎American Dragnet: Data-Driven Deportation in the 21st Century
Nina Wang, Hannah Bloch-Wehba, et al., Georgetown Law Center on Privacy and Technology
May 2022 ↩︎Global data centre electricity consumption reached approximately 415 TWh in 2024. See: Energy and AI – Energy Demand from AI
International Energy Agency (IEA), 2025 ↩︎The Fiction of The Wired: Loneliness and the Limits of the Internet
Marlin Figgins, University of Chicago Smart Museum
2020 ↩︎Serial Experiments Lain – Layer 04: Religion
↩︎1998 Understanding Phantom Tactile Sensation on Commercially Available Social Virtual Reality Platforms
Qijia Chen, Michiel M. Spapé and Giulio Jacucci, Proceedings of the ACM on Human-Computer Interaction, Vol. 8, CSCW1
April 2024 ↩︎Nonverbal Overload: A Theoretical Argument for the Causes of Zoom Fatigue
Jeremy N. Bailenson, Technology, Mind, and Behavior (APA), Volume 2, Issue 1
2021 ↩︎Video-Conferencing Usage Dynamics and Nonverbal Mechanisms Exacerbate Zoom Fatigue, Particularly for Women
Géraldine Fauville, Jeff Hancock, Anna Queiroz, et al., Computers in Human Behavior Reports
2023 ↩︎Delusional Experiences Emerging From AI Chatbot Interactions or "AI Psychosis"
Alexandre Hudon and Emmanuel Stip, JMIR Mental Health, 2026 ↩︎The Turk: The Life and Times of the Famous Eighteenth-Century Chess-Playing Machine
Tom Standage, Walker & Company, 2002 ↩︎ELIZA – A Computer Program For the Study of Natural Language Communication Between Man and Machine
Joseph Weizenbaum, Comms. of the ACM, Vol. 9, No. 1, January 1966 ↩︎Preliminary Report on Chatbot Iatrogenic Dangers
Allen Frances and L. Ramos, Psychiatric Times, 15 August 2025 ↩︎AI companion apps on track to pull in $120M in 2025
Sarah Perez, TechCrunch
12 August 2025 ↩︎Lawsuit claims Character.AI is responsible for teen’s suicide
Angela Yang, NBC News
23 October 2024 ↩︎How I Found (Some) Empathy for the Reddit AI Boyfriend Community
Annabel Iwegbue, Cosmopolitan
10 September 2025 ↩︎“Lessons From an App Update at Replika AI: Identity Discontinuity in Human-AI Relationships”
Julian De Freitas, Noah Castelo, Ahmet Kaan Uguralp, Zeliha Oğuz-Uguralp, Harvard Business School Working Paper
2024 ↩︎“’Death’ of a Chatbot: Investigating and Designing Toward Psychologically Safe Endings for Human-AI Relationships”
Rachel Poonsiriwong, Chayapatr Archiwaranguprok, Pat Pataranutaporn, MIT Media Lab
February 2026 ↩︎‘I was heartbroken’: Dealing with grief when your AI lover is shutdown
Camille Bello, EuroNews
14 December 2023 ↩︎The Rise of AI Companions: How Human-Chatbot Relationships Influence Well-Being
Yutong Zhang, Dora Zhao, Jeffrey T. Hancock, Robert Kraut, Diyi Yang, Stanford University & Carnegie Mellon University
16 June 2025 ↩︎“My Boyfriend is AI”: A Computational Analysis of Human-AI Companionship in Reddit’s AI Community
Pataranutaporn, P., Karny, S., Archiwaranguprok, C., et al., MIT Media Lab & Cornell
14 September 2025 ↩︎The Para-Real: A Manifesto
Cade Diehm, New Design Congress
10 December 2022 ↩︎
↩︎ Games of Empire: Global Capitalism and Video Games
Games of Empire: Global Capitalism and Video Games
Diesel ‘Bucket Brigade’ Keeps Peer 1 Online at 75 Broad
Rich Miller, Data Center Knowledge
31 October 2012 ↩︎OVHcloud Fire Investigation Report
Bureau of Investigation and Analysis of Industrial Risks (BEA-RI), Bas-Rhin firefighters
2022 ↩︎Kakao Suffers Worst Server Outage, With No Complete Recovery in Sight
The Korea Herald
16 October 2022 ↩︎A Chilling Russian Cyber Aim in Ukraine: Digital Dossiers
The Associated Press, NBC News
2022 ↩︎Three Digital Boxes That Saved Ukraine’s Government Data
The Irish Times
8 December 2022 ↩︎Google Cloud Incident #dS9ps52MUnxQfyDGPfkY
Google Cloud
25 April 2023 ↩︎ERCOT Blackout 2021
Energy Institute, University of Texas at Austin, 2021 ↩︎Texas Data Center Expansion Raises Blackout Risk During Extreme Winter Weather
CNBC, 22 November 2025 ↩︎National Security Law Casts a Shadow Over Hong Kong’s Art Scene
The Diplomat, March 2021 ↩︎Internet Archive Services Update: 2024-10-21
Internet Archive
21 October 2024 ↩︎WG 15 - Background to ISO/IEC 2382
ISO/IEC JTC 1/SC 15 Working Group
2025 ↩︎IEEE Standard Glossary of Computer Hardware Terminology (IEEE Std 610.10-1994)
Institute of Electrical and Electronics Engineers (IEEE)
1994 ↩︎The von Neumann Architecture - Dive Into Systems
Suzanne J. Matthews, Tia Newhall, Kevin C. Webb
Current edition ↩︎Improving Gmail Labels with the Affordances of Folders
Google Research, CHI 2010 Conference Proceedings
April 2010 ↩︎‘Everything on the internet can be saved': Archive Team, Tumblr and the cultural significance of web archiving
Jessica Ogden, Internet Histories, Vol. 6, Issue 1-2
21 October 2021 ↩︎A meme celebrating the prevalence of gay content on Tumblr.
iamuaremod (original author unknown), Tenor ↩︎Archive Team: A Distributed Preservation of Service Attack, DEFCON 19
Jason Scott
6 August 2011 ↩︎Tumblr will ban all adult content on December 17th
Hacker News
3 December 2018 ↩︎Burning the Library
Cory Doctorow, Boing Boing
19 December 2018 ↩︎Pornography, Trans Visibility, and the Demise of Tumblr
Carolyn Bronstein, TSQ: Transgender Studies Quarterly, Duke University Press
2020 ↩︎Tumblr Is Betraying The Sex Workers And NSFW Artists Who Relied On The Platform
Julia Craven, HuffPost
December 2018 ↩︎Archive Team: Robots.txt
Archive Team Wiki ↩︎ICE Wants to Go After Dissenters as well as Immigrants
Brennan Center for Justice
2025 ↩︎
↩︎ The Years of Rice and Salt
The Years of Rice and Salt
2002 Case Study: Napster: Opportunity Meets A Web of Egos
John Glynn Jr. & Alex Tauber, Stanford Graduate School of Business
2009 ↩︎uTorrent Turns 10 Years Old Today
Ernesto Van der Sar, TorrentFreak
18 September 2015 ↩︎Pirate politics between protest movement and the parliament
Martin Fredriksson Almqvist, Ephemera Journal
2016 ↩︎File Sharing, Network Architecture, and Copyright
Tilman Klumpp, University of Alberta
May 2013 ↩︎This Is Fine: Optimism & Emergency in the P2P Network
Cade Diehm, New Design Congress
16 July 2020 ↩︎Pirate Bay co-founders’ criminal conviction for assisting copyright infringement on the Internet was justified
European Court of Human Rights (ECHR)
13 March 2013 ↩︎Software Piracy Ringleader Extradited from Australia
U.S. Department of Justice, Office of Public Affairs
20 February 2007 ↩︎Spotify CEO Daniel Ek says working musicians may no longer be able to release music only "once every three to four years"
Jordan Darville, The FADER
30 July 2020 ↩︎Spotify’s Daniel Ek leads €600mn investment in German drone maker Helsing
Financial Times
16 June 2025 ↩︎Scene rulesets are distributed as plaintext documents within releases. Representative examples – including category-specific standards for MP3, FLAC, x264, and television – are archived at scenerules.org. ↩︎
Chapter 5 - Subculture of the Subcultures
Copyright Does Not Exist
Linus Walleij (translated by Daniel A. Øien)
1998 ↩︎If a do-gooder attempts to mirror myrient into the Internet Archive I will personally be at the foot of your bed when you next wake up.
@textfiles.com on Bluesky
28 February 2026 ↩︎Diaspora Communities Reframe History, One Instagram Post at a Time
Andrew Deck and Kisha Ravi, Rest of World
28 June 2022 ↩︎Social Media Platforms Block Hashtags That Brought Attention To Sri Lankan War Crimes
Kaya Kannan, Human Rights Pulse
15 March 2021 ↩︎Furry acts as non/human drag: A case study exploring queer of colour liveability through the fursona
Hazel (Bobbi) Ali Zaman, Queer Studies in Media & Popular Culture, Volume 8, Issue 1
April 2023 ↩︎The User’s Guide to Gridism (v.2.0)
K. Guillory, Medium
20 May 2016 ↩︎Call for an MMO-Based Art Movement Called ‘Gridism’
Wagner James Au, New World Notes
November 2016 ↩︎LGBTQ+ Activism in 1970s & 1980s NYC
New York City Department of Records and Information Services
Revised July 2024 ↩︎Violence Against and Policing of LGBTQ Communities: A Historical Perspective
Courtenay W. Daum, Oxford Research Encyclopedia of Politics
26 April 2019 ↩︎1970s punk rock: a ‘fuck you’ to the spatial homogenization of New York City
Chapin Cassidy Dorsett, Whitman College
2019 ↩︎Queer Law and Order: Sex, Criminality, and Policing in the Late Twentieth-Century United States
Timothy Stewart-Winter, Journal of American History
2015 ↩︎